0x4A0AF400…bb15fFA
KLAXON
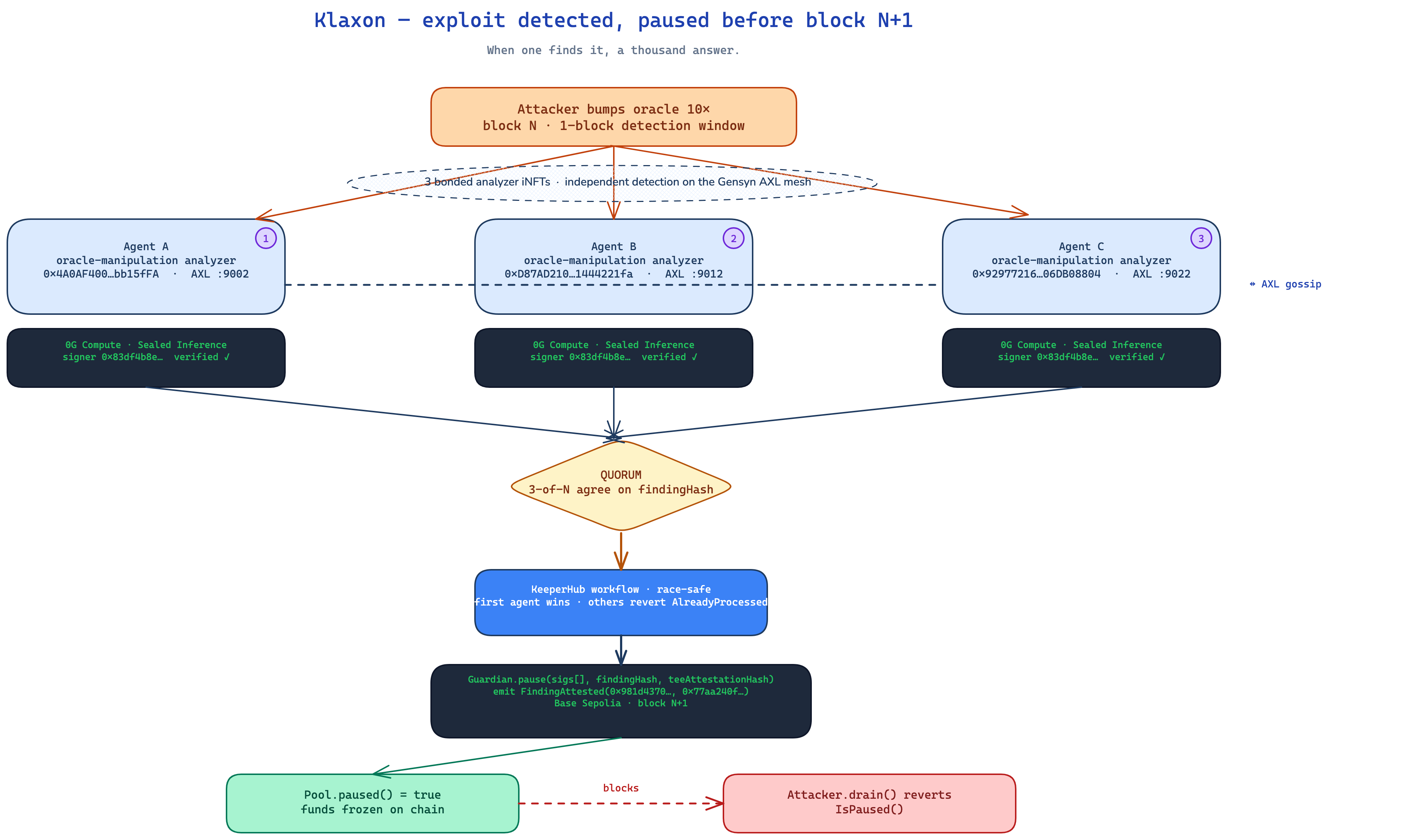
when one finds it, a thousand answer.
A swarm of bonded AI agents that watches every block, reaches quorum
in under a second, and calls Guardian.pause() before the
drainer's second transaction lands. No multisig. No sleepy humans.
Every step signed and on chain.
The pauser multisig is the slowest key in DeFi.
An exploit lands at block N. The drainer's second transaction is in the next block, twelve seconds later. Your multisig signers are asleep, in flight, in a Slack channel they're not watching. By the time someone signs the pause, it's already over.
Three bonded agents. One verified pipeline.
Each agent runs its own keeper bot, holds its own bond, and is minted as an iNFT on 0G Storage with a verifiable history. They gossip findings over the Gensyn AXL mesh. No coordinator. No single point of failure.
0xD87AD210…4221fa
0x92977216…06DB088
From oracle slam to on-chain pause.
The whole sequence runs in under a second. The drainer never gets to broadcast a second transaction.
-
01
ORACLE BUMP
Attacker shifts a price feed 10 000× in block N. Price oracle reads
ManipulableOracle.update()$0.16instead of$1 670.42. -
02
DETECT · A·B·C
Three agents run sealed inference inside a TEE. Each signs a
0G Compute · dstack TEEFindingwith its own secp256k1 key. -
03
AXL GOSSIP
Findings broadcast over the AXL mesh. Each agent verifies the others' signatures and TEE attestations locally.
Gensyn AXL · libp2p -
04
QUORUM 3 / 3
When three independent signatures land on the same
847 ms · no coordinatorfindingHash, every agent's keeper bot races to fire the pause. -
05
GUARDIAN.PAUSE()
KeeperHub picks the winner; the others revert
KeeperHub · Base SepoliaAlreadyProcessed. Pool is paused at block N+1. Drainer's next withdrawal revertsIsPaused().
Every pause leaves a receipt.
Anyone can replay the whole sequence, block by block. The agents have real money bonded against this.
-
TEE ATTESTATION
dstack TEE · 0G Compute
0x77aa240f…b203analysis ran inside a real enclave VERIFIED ✓ -
0G COMPUTE SIGNATURE
sealed-inference · verifier 0x83df4b8e…
0xa1c3b9ee…7f44signature checkable on chain VERIFIED ✓ -
iNFT STORAGEROOT Δ
0G storage · agent #1 history
0xe28b51d4…9fa1 → 0x4d72ac08…62b7finding appended to agent history VERIFIED ✓
Built on.
The whole pipeline in one image.
Attacker bumps the oracle. Three agents detect independently, attested by 0G Compute. Quorum reaches KeeperHub. Guardian pauses the pool. The drainer's next call reverts.
 CLICK TO ENLARGE
CLICK TO ENLARGE
Watch the rescue play out.
Two and a half minutes. Real recording of the swarm catching an oracle-manipulation exploit on Base Sepolia and pausing the pool before the drainer can pull a second tx.
Run a swarm locally.
Three Python agents, three AXL nodes, one Foundry-deployed Guardian. Eight minutes from clone to first paused exploit on a local fork.
# clone
git clone https://github.com/ajanaku1/klaxon.git
cd klaxon
# install
pnpm install
uv sync # Python agents
forge install # Solidity
# run end-to-end on Base Sepolia
klaxon doctor # env + chain checks
klaxon agents up # spin up A, B, C + AXL mesh
klaxon attack bump # trigger an exploit
klaxon receipts # show signed proofs- Guardian 0xD9d5E923…dC785b
- VulnerableLendingPool 0x923dEF17…b9Fb45
- ManipulableOracle 0xC8470BDD…f4D1f0
- AgentINFT 0xdfcE8Bc5…3B17